What is digital rights management? All you need to know
Last updated
9 Mar
2026
By
Steffin Abraham
Duration
x
min
Published on
16 Jun 2023
By
Marvellous Aham-adi

Modern technology has made digital piracy so much easier. With a few clicks of a button, people can download digital assets from the internet, then proceed to edit and use them as they please – often without the permission of the owner. For example, in France alone, almost 12 million people are illegally downloading and streaming videos.
Digital piracy is such a significant issue that Motion Picture Association (MPA) reports that the US economy loses up to $29 billion annually just from online TV and movie piracy. Software companies also lose close to $359 billion annually from unlicensed or counterfeit software.
It’s also not just the government and companies that suffer from piracy. In the music industry alone, 70000 people lose their jobs annually because of the revenue lost from music piracy.
The customer experience is also affected. This is because most of the time the pirated content isn’t usually up to the same standard and quality as the original content. So not only is the customer not getting full value, the owner of the original content may get a poor reputation.
This is where digital rights management comes into play. It offers a solution for businesses and creators to protect their digital assets. So in this article, we will see all you need to know about digital rights management.
Let's get started.
What is digital rights management?
Digital rights management (DRM) is the process involved in protecting and restricting the use of copyrighted digital assets. DRM uses a variety of methods and technologies to control how digital assets are used, edited, and shared online.
Examples of assets that can be protected by DRM include:
- Copyrighted media content like images, videos, and audio.
- Intellectual property like patents, product plans, trademarks, and trade secrets.
- Confidential documents like financial records or policy documents. Licensed documents like ebooks and digital subscriptions can also be protected by DRM.
- Copyrighted software like operating systems and applications.
These are some examples of the assets that DRM tools are designed to protect.
DRM may also be called technological protection measures (TPM). And there are two types of TPM:
- Access control measures which restrict unauthorized individuals access to a work, and
- Copy control measures which restrict what can be done with the work.
How digital rights management works
Digital assets are protected by copyright laws. This doesn't mean that they will automatically be safe from illegal use because most people do not abide by these laws. Monitoring the web to see who is using your assets illegally can also be very time-consuming and challenging. Using a DRM tool will help you easily protect digital assets from theft.
DRM tools use encryptions and restrictions to help limit access or usage of digital content. These restrictions include:
- Password protection: This is a simple but effective way to protect digital files. Users must input the set password before they can access the file.
- Copy protection: This restriction allows a user to view or consume a piece of content only on the channel it was shared. The DRM will prevent the user from making a copy. For example, if you implement this type of DRM on your website, users won’t be able to save images, copy texts, or make screenshots.
- Copy prevention: This is similar to copy protection. The only difference is that the user can be allowed to make copies only if certain conditions are met or if they agree to your terms and conditions. For example, a user may be allowed to make copies only if they have agreed not to sell it commercially. You can even set expiration dates for your content or open limits; how many times a user can open or view content.
- Watermarks: A DRM can add watermarks to your photos, videos, and GIFs. Users can download these assets but won’t be able to use them for commercial purposes.
- Device control: These restrictions ensure that files are only opened on approved devices. You can even restrict access to your content based on the user's location and IP address.
Benefits of digital rights management
Some of the benefits of DRM have already been highlighted in the previous section. Let's take a look at some other unique benefits that businesses and creators gain from implementing DRM in their business.
1. It enforces copyright laws
DRM tools restrict where and how a user can use copyrighted digital assets. They can alter or reduce the performance of content if they suspect it is being used without authorization. For example, Spotify adds a DRM layer to songs so users cannot listen to the songs anywhere except on their apps. The DRM layer scrambles the audio data and only the Spotify player can play the unscrambled version.
Some tools can even monitor purchasers and will report on when and who accessed the content and how it was used. And coupled with the Digital Millennium Copyright Act (ACT), a copyright owner can then takedown services or websites that are sharing their works without permission.
2. Optimizes collaboration between teams and with third parties
There are security risks involved when sharing data assets with third parties outside of your organization. DRM helps you significantly reduce these risks because it clearly defines what assets are available for use and how they can be used. You can even monitor when a user has attempted to share the digital asset with other people without authorization.
3. DRM is critical for data security
DRM helps businesses restrict access to sensitive documents and confidential information by using encryption combined with licensing. And even when they are data leaks, DRM technology makes it easy to track these leaks.
4. Helps businesses follow regulatory compliance
Depending on the business type and its location, there are laws, regulations, and guidelines that every organization must comply with. Failing to comply with these regulations often results in legal punishments like fines. DRM ensures that businesses follow and maintain regulatory compliance.
For example, laws like GDPR expect businesses to guarantee that the personal information of their users is safe. The Sarbanes-Oxley Act or the Health Insurance Portability and Accountability Act (HIPAA) even requires that you demonstrate that you have the proper processes in place to protect this sensitive information.
A DRM tool will ensure that documents containing this sensitive information are safe even if they are stored on computers or when they are distributed outside of your organization.
5. Helps creators monetize their content more efficiently
DRM technology allows content creators to be able to efficiently monetize their content or digital assets with the use of licensing contracts and agreements. Creators can license out their work in exchange for monetary compensation. So whenever someone uses the creator’s content, they get some revenue.
Features to look for in DRM software
Before you invest in DRM, there are certain factors you should consider to guarantee you choose the right software for your business.
1. Content protection and encryption
If your content can be easily copied, shared, or printed, it is at the risk of piracy, plagiarism, mass redistribution, and intellectual property infringement. Just adding password protection to your files wouldn’t guarantee their safety. And while adding watermarks can help reduce copyright infringement, it isn’t an absolute solution.
The most effective solution is to choose a DRM that offers strong encryption that makes your content unreadable unless the user has an encryption key or is on an authenticated system. This will help protect your files from hackers and unauthorized sharing.
2. User access control

Source: AssuranceLab
A comprehensive digital rights management solution should allow you to set up different types of user controls. Some of these controls include:
- Start date - this is the date when a user can first access a piece of content. Before this date, the content will be unavailable
- Expiration limits - the content automatically expires after a set amount of time
- Print limits - this limits how many times a user can print your content
- Open limits - limits how many times a user can open and view content
- Device/browser limits - limits how many devices or browsers a user can open content on
And along with being able to set up different access control policies for both your team and external stakeholders, your DRM software should give you the ability to revoke a users’ access to your digital assets at any time.
3. User/content analytics and tracking
After setting up your DRM system, implementing access controls, and protecting your content, you also need to monitor how your content is used. Choose a software that offers detailed analytics reports. It will give you insights into how your users are engaging with your content and also help you quickly identify possible suspicious activity.
For example, if a user accesses your content with different browsers, IP addresses, or even countries in a short amount of time, it could be a sign that the user is doing something shady with your content. You can easily stop this by applying some of the limits mentioned above.
4. Integration with third-party systems
Your DRM software should integrate easily with other websites or third-party systems like digital asset management systems (DAM), content management systems (CMS), eCommerce systems, business intelligence systems, customer relationship management systems (CRM), learning management systems (LMS), etc. Integrations ensure that there is communication between the business tools you use. This will lead to increased data consistency and productivity.
5. Smooth end-user experience
The easier it is to use the DRM, the more effective and productive your teams will be. Avoid tools that will require you to download a bunch of plugins or apps before they can be used. You don’t want software that will disrupt the user experience of your team members, subscribers, partners, or clients.
Best practices for digital rights management
As digital piracy becomes increasingly rampant, DRM is very important as it keeps your digital assets safe and secure. And most businesses know this too. This is why the global digital rights management market size was valued at over $4.5 billion in 2021 and is expected to reach $12 billion by 2027 at a CAGR of 17.64%. (CAGR - Compound Annual Growth Rate)
To ensure that you don’t fall behind or waste your investments, here are some DRM best practices you should follow.
Implement DRM only on the right kind of content
You don’t have to use DRM on all the content or digital assets you publish. A con to using DRM is that it can reduce the reach and engagement level of your content. For example, if you placed location-based restrictions on a video, only people in that location will be able to play the video. If you want to reach a large number of people, using this type of restriction isn’t the best option.
Always ask yourself what the purpose for creating the content or digital asset is. If it’s to boost awareness or business reach, then use fewer restrictions. Restrictions are great for monetizable content or digital assets you want only people with permission to view.
Manage external contracts
DRM can be used to manage contracts with external parties associated with your visual content. From photographers to models, information related to the correct distribution of your images can be easily found and kept up to date. This means that if you’re not sure if a certain image can be used in a particular territory, you’ll be able to access that information straight away without having to bother other teams.
What’s more, with the help of reverse search you can check if any of your images are being used illegally or breaking copyright laws.
Integrate it with other digital management solutions
To get the full benefits of your DRM, it’s important to integrate it with other infrastructures for managing data like Digital Asset Management (DAM), data loss prevention (DLP), and content management solutions (CMS).
For example, a DLP solution will prevent potential data leaks or loss by restricting the sharing of data in certain conditions. So while your DLP tool enforces data protection protocols for your organization's sensitive data assets, your DRM allows you to securely share files and revoke access to users when required.
Educate your employees about DRM
Your DRM won’t be as effective if your employees are not properly educated on its importance. For instance, an employee who doesn’t understand how critical digital rights management is might share passwords to sensitive assets with unauthorized users. This can lead to leaks and piracy issues.
Just restricting how employees use and share digital assets isn’t enough. They need to be educated on why they are restrictions and the negative impacts they could have on your business when it’s not followed.
Combat shadow IT
Shadow IT is the use of information technology systems, applications, software, devices, and services without the knowledge or approval of the IT department. It is a big security risk for companies that deal with sensitive information and can make it extremely difficult to track how data is used and shared.
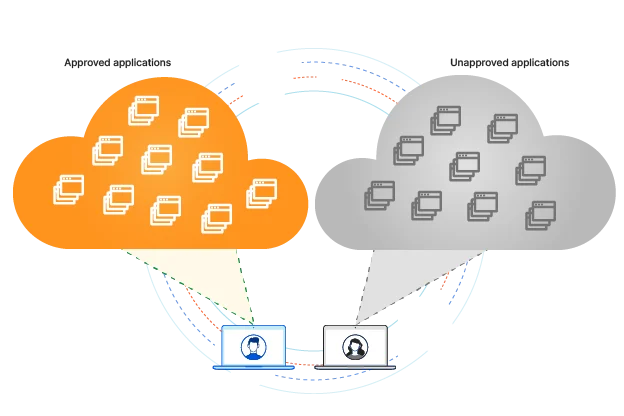
Source: Cloudflare
Shadow IT occurs when employees start to use unauthorized devices for work, share files via unsecured channels, or when they install apps that are not compliant with the organization’s IT policy. All these practices expose your business to leaks and breaches. So, it's best practice to minimize how much shadow IT occurs in your company. This will help reduce the workload on your DRM.
How can your combat shadow IT?
First, make sure all your employees understand what shadow IT is and its risks.
DLP tools can also flag your IT team whenever someone tries to move sensitive data from a secured corporate system to any unauthorized system. This will help them take appropriate action before there is a breach.
Combining DRM and DAM
A Digital Asset Management (DAM) solution allows organizations to efficiently store, manage, and deliver their digital assets. And since a DRM functions to protect the rights to those digital assets, it is only logical that you integrate your DAM system with a DRM solution.
Most times, you won’t even have to invest in two tools. A good DAM system like Wedia comes with powerful DRM features that will help you control access to your digital assets. With user permissions, you can control everything a user does, sees, or interacts with in the DAM
You will be able to securely share assets with employees and external collaborators while complying with usage rights. Copyrighted information is also attached to each asset along with picture and video watermarking capabilities to ensure that your content isn’t used without authorization.
Within the DAM library, you can also add digital rights information to your assets. It offers users with information on how to use each asset. This information includes things like model rights, location rights, expiration dates, and limitations if there are any. This information serves as rules so that your team and external parties stay in compliance.
When uploading digital content to Wedia, you can even add expiry dates. The DAM sends notifications to users to let them know not to use images after a certain date
Wedia will also allow you to organize a large volume of assets and their variations using advanced indexing capabilities. Applying metadata allows you to segment content while AI auto tags and metadata extraction such as text, emotion, or facial recognition make it easy to quickly find any content you need.
On top of that, you can still integrate a dedicated DRM to Wedia DAM for more advanced capabilities. To learn more about Wedia DAM, book a free demo.
Key Takeaways
- Digital Rights Management secures high-value assets through encryption and access restrictions.
- DRM is essential for regulatory compliance with GDPR, HIPAA, and Sarbanes-Oxley.
- Large businesses use DRM to prevent unauthorized sharing and protect brand reputation.
- Integrating DRM with a DAM solution automates rights tracking and usage notifications.
- Effective DRM implementation requires educating employees to minimize the risks of shadow IT.
Frequently Asked Questions
Q: How does digital rights management differ from copyright law?
A: Copyright law provides the legal framework for ownership, while DRM provides the technological means to enforce those rights. DRM prevents the act of piracy before it occurs through encryption and access controls.
Q: Is DRM necessary for all digital content?
A: No, DRM should be used selectively. Global brands often use DRM for proprietary software, confidential documents, and monetizable media, while leaving awareness-driving content more accessible.
Q: Can DRM track who is using my images illegally?
A: Yes, modern solutions use reverse image search and watermarking to identify where assets are published online. This helps brands take action against unauthorized use and intellectual property infringement.
Q: How does DRM help with GDPR compliance?
A: DRM ensures that sensitive documents containing personal data are encrypted and only accessible to authorized users. This fulfills the GDPR requirement to protect data during both storage and distribution.
Q: Will DRM affect the user experience of my customers?
A: A well-implemented DRM solution should be seamless. By using a modern DAM with native rights management, you can ensure authorized users have fast access without needing complex third-party plugins.
Q: Can I revoke access to an asset after it has been shared?
A: Yes, professional DRM tools allow administrators to revoke access tokens or expire links at any time. This is critical for crisis management or when a licensing agreement ends unexpectedly.
Q: What are the risks of shadow IT in rights management?
A: Shadow IT leads to assets being shared over unsecured channels where DRM cannot be enforced. This increases the risk of data breaches and unauthorized redistribution of sensitive company information.
Q: How does AI improve digital rights management?
A: AI can automatically extract metadata related to model rights and usage terms. This ensures that assets are correctly categorized and indexed, making it easier to manage compliance at a global scale.
Bottom Line
Digital Rights Management is a critical pillar for any global brand looking to protect its intellectual property and maintain regulatory compliance. By integrating DRM capabilities directly into your DAM, you create a secure, automated environment that protects your revenue and your reputation.
Call to Action
See how Wedia helps global brands solve digital rights management challenges and protect their high-value media. Book a personalized demo today for a strategic consultation.


